Amazon Connect is a fully managed, cloud-based Contact Center as a Service (CCaaS) offering from AWS. It provides an easy-to-use, scalable platform for voice and chat-based customer interactions, with pay-as-you-go pricing and built-in integrations with AWS AI services like Amazon Lex (for chatbots), AWS Lambda (for custom logic), and Amazon S3 (for call recordings and data storage). There's no upfront hardware or licensing costs.
To enhance user experience and streamline access management, organizations can integrate Amazon Connect with Microsoft Entra ID (formerly Azure AD) to enable Single Sign-On (SSO). This integration allows agents, supervisors, and administrators to access Amazon Connect and related AWS services using their existing corporate credentials—eliminating the need to manage separate usernames and passwords.
Scenario Overview:
A customer needed to deploy an Amazon Connect instance that could federate users from their existing Office 365 environment by leveraging Azure Active Directory (Entra ID) for centralized identity management. The requirement was to host Amazon Connect within their existing AWS account and restrict access to designated users within a specific environment.
While Amazon Connect can integrate with Active Directory through AWS Directory Service. In this case, it made more sense to leverage the customer’s existing identity provider.
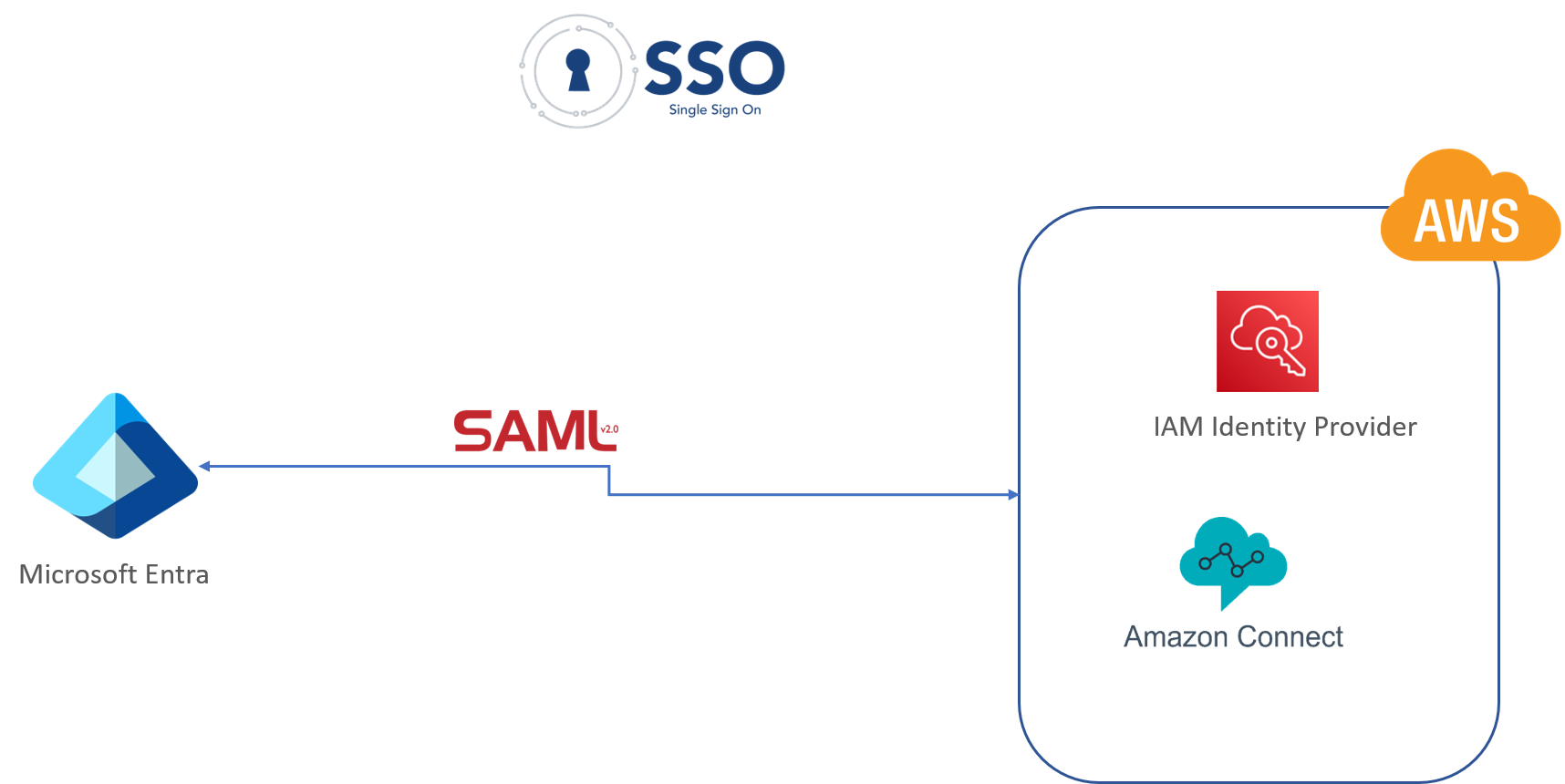
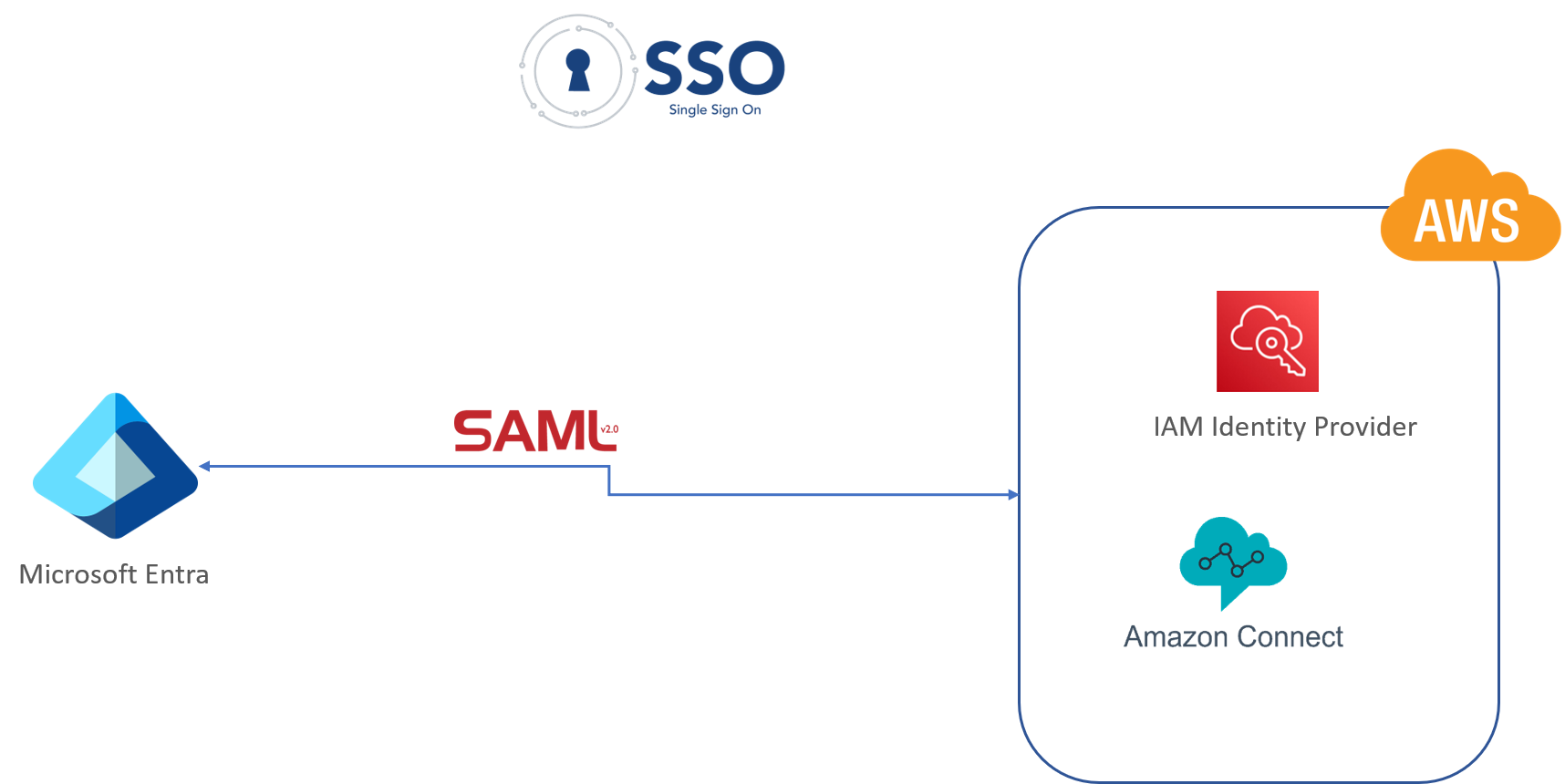
Instead of using AWS IAM Identity Center (formerly AWS SSO)—which requires changes at the AWS Organizations level and could affect the broader infrastructure—we chose to configure an AWS IAM Identity Provider within the target environment. This approach provides strong support for SAML-based authentication and enables single sign-on access specifically to the designated environment.
Since Amazon Connect does not natively integrate with IAM Identity Center, the chosen approach involved configuring a SAML identity provider in the target AWS account using the SAML metadata generated by an Entra ID application.
Amazon Connect & Azure AD (Entra) SSO Set-up
Azure AD (Entra) SSO Set-up
Prerequisite:
Azure AD (Entra) Admin Center access
Process:
Log into the Azure Active Directory admin center
Select “Enterprise Applications”
Select “Create your own application” and give it a unique name
Create an enterprise application (Example: "amazon-connect-sso")
Create your own application - Screen Image
Once the application is ready, proceed to configure Single Sign-On by opening the menu and selecting the "SAML" option
Download Federation metadata file from Azure AD (Entra) - To be uploaded into AWS IAM Identity Provider configuration
Click the download link for the “Federation Metadata XML” and save the file securely. Do not share this file with anyone!
Create user Group and assign SSO candidate users to the group. (Only users assigned to this group would have SSO access to Amazon Connect after they are added into Amazon Connect)
Add users to the SSO application to activate their access
Create Two Custom Roles
Role 1
Role 2
Amazon Connect Set-up
Prerequisite:
Access to AWS for setting up Amazon Connect
Process:
Create Amazon Connect Instance with SAML instance type (Out of 3 options available 1- CONNECT_MANAGED, 2- AWS Active Directory, and 3- SAML)
*Create admin user with same details with already existing user credentials in Azure AD (Entra)
AWS IAM for SSO Set-up:
Prerequisite:
Access to AWS IAM
Process:
Create and Configure an Identity Provider in AWS IAM
Upload Federation metadata file from Azure AD (Entra) into AWS IAM Identity Provider - from application (Example: "amazon-connect-sso") created in Azure AD (Entra).
Create an IAM Role and Policy for SAML Federation
Note: All set-up can be in IaC (Infrastructure as Code) using AWS CDK